Table of Contents
We won’t talk about the theory of DevSecOps, but rather about tips and concrete ways to integrate it into your development cycles and improve your security.
DevOps, DevSecOps, digital transformation… Words that have been on everyone’s lips for the past few years, and whose trend is not decreasing. According to Cesin‘s Corporate Cybersecurity Barometer (January 2020), 89% of companies surveyed use the cloud to store part of their data, and 55% do so with a public cloud.
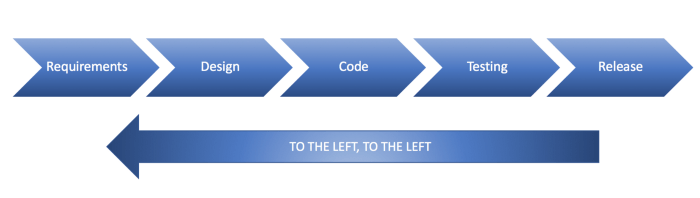
In this context of digital transformation, new modes of organization and tooling are disrupting development and production teams. The DevSecOps approach consists of integrating security throughout the Software Development Life Cycle (SDLC). The objective is to secure products as early as possible in order to limit costs for the company. The later a vulnerability is discovered, the more costly it will be for the organization.
1. Integrate DevSecOps tools into your pipeline
The DevSecOps approach brings together two seemingly opposite objectives: a fast delivery and a secured code. With the “Shift Left” methodology of DevSecOps, teams can reduce the impact of vulnerabilities by discovering them early in the process.
Automation is a key component of DevSecOps: automating security testing empowers teams and accelerates vulnerability detection and remediation. It is therefore essential to adopt specialized DevSecOps tools.
Vulnerability scanners such as Acunetix are very efficient to perform a first audit of your information systems. Static code analysis tools like Codacy or SonarQube are also a good start for spotting the most obvious defects.
There are plenty of DevSecOps tools available, so you shouldn’t have any trouble finding one to match your pipeline and budget. This list of 9 DevSecOps tools for your development teams by Mend is a good starting point.
2. Choose flexible security solutions that fit your development cycles
Penetration Testing and Bug Bounty are complementary solutions to automation. These audits are essential to maintain a good level of security, while integrating the human factor. These 2 approaches allow companies to identify more critical vulnerabilities, by involving consultants or skilled hackers.
Agile development cycles require the adoption of flexible security solutions. To implement an efficient DevSecOps approach, one must be able to test products at the time of their conception. Software vendors are particularly challenged by this evolution.
It’s becoming obvious that you have to be in a reactive and proactive security, especially when you’re a SaaS solution, with a code that evolves quickly. Jenji makes about 30 releases a month, so it’s possible that there are regressions, differences from one API to another.
– Pierre Quiennec, CEO of Jenji
Bug bounty: a flexible and time-saving audit that fits into the DevSecOps culture
One of the benefits of Bug Bounty is that it allows you to launch tests quickly. In 1 or 2 days you can write your program and define the targets to be tested, while the platform takes care of finding hackers that meet the requirements
The speed of implementation of this approach fits perfectly with the DevSecOps culture. Also, Bug Bounty can be launched in the pre-production phase, but also in the production phase during the product life cycle.
For our digital activities, the interest of bug bounty lies in the flexibility of its use and its speed of activation. Bug bounty programs are launched in 1 or 2 days, the time saving is considerable.
– Richard Guidoux, CISO Thalès Digital Factory
3. Raise awareness and train your teams in offensive security
Choosing the right security solution for your development cycles is not enough. Your teams are at the heart of a successful DevSecOps approach. And we’re not just talking about developers, security teams are also involved. This approach brings the idea that all collaborators are responsible for the security of an organization.
So, how do you get your people on board and trained in DevSecOps? Many methods exist to teach your teams about security, here are some of them:
- Offer your collaborators to participate in conferences on cybersecurity or hacking (DefCon, Blackhat, RSA Conference…)
- Organize a workshop between your security teams and the others
- Set up a monitoring unit within your organization and encourage your staff to read vulnerability reports published by hunters
- Offer cybersecurity training to your people
- Encourage your teams to participate in CTFs (e.g. 0CTF, PlaidCTF, DefCon CTF, CSAW) or bug bounty programs
How does Bug Bounty help train teams in offensive security
Bring a new security culture to your company, by encouraging your employees to participate in CTFs or Bug Bounty programs. You can also choose a Bug Bounty platform to secure your IT perimeters and train your teams to exploit vulnerabilities.
On the Yogosha platform, hunters do not only interact with security teams, but also with customers’ development teams. We provide customers with dashboards with statistics on which vulnerabilities have been found the most, which allows them to know where their development teams’ weaknesses are, and to provide them with appropriate training on the detected vulnerabilities.
– Mohamed Foudhaili, Security Specialist & Technical Program Manager at Yogosha
By encountering vulnerabilities they have never seen before, or by seeing the ingenuity of hackers in attacking subsystems, bug bounty collaborators understand that the attack surface is larger than it appears, and they will rethink these attack patterns when designing or implementing new systems. Teams gain expertise in exploiting vulnerabilities by working with experienced hackers and trying to replicate the attacker’s thinking.

As for the profile of the hackers, it varies from one platform to another. Regarding Yogosha, we have a private community model with prior selection. The identity of each member of the Yogosha Strike Force is verified, and researchers must pass tests to validate their technical and pedagogical skills. Only 20% of candidates are accepted at each session. This allows our clients to benefit from the highest level of expertise on the Bug Bounty market.
A rigorous and controlled selection of a private group of hunters now makes it possible to define and implement managed Bug Bounty programs on sensitive systems. Sopra Steria manages all phases of preparation, execution and remediation, enabling the capitalization of best practices. In addition, the implementation of internal programs enables the detection and stimulation of our customers’ talents.
– Geoffroy Cécile, Cyberdefense Technical Director at Sopra Steria
Looking for DevSecOps friendly audits like Bug Bounty or Pentest as a Service?




