Launch pentests agilely and continuously across your SDLC
Assess your assets’ digital security and reduce their likelihood of being compromised.
What is Pentest as a Service?
Test your assets’ digital security
Penetration testing as a service (PtaaS) is a technical security audit that enables organizations to deploy a small team of skilled security researchers to test the robustness of their assets and meet compliance.
Why PtaaS?
Old School made new
Traditional pentesting is no longer suited to organizations’ modern development cycles, nor to the rapid growth of digital threats. Old-school pentests lack flexibility, cost-effectiveness and firepower.
It’s like the pentest you’re used to, but better.
Agile and point-in-time security testing
With a hacker mindset
With PtaaS, you can test your assets on-demand and at any time across your SDLC. Our pentests are agile and adapted for DevSecOps, whether you’re looking to test assets before a release or live in production.
- Work with top performing security researchers only
- Launch tests within days, not weeks
- Agilely launch multiple pentests all year long
Additional benefits of PtaaS
More reasons to go with Yogosha
Security researchers continuously monitor your assets and use the latest tools, tactics and procedures (TTPs) to find critical and complex vulnerabilities.
- Find critical vulnerabilities and get remediation guidance
- Assess your assets’ risk profile periodically
- Helps for compliance and legal requirements
- Showcase robustness of your products to your clients / investors
By getting access to the right security researchers, you increase the odds in finding critical vulnerabilities.
Our dedicated team accompanies you along your Offensive Security journey for expert advice and optimized results.
A certificate is delivered after each pentest. Use it to promote your security policies to your partners & clients.
The Yogosha Strike Force
800+ security researchers
Vetted and highly skilled
Only 10% of applicants are accepted into the Yogosha Strike Force (YSF). Our security researchers passed a technical and redactional test — which makes for clear and fully documented vulnerability reports. They’re also ID checked, and signed T&Cs with an NDA.
Skilled in multiple asset types:
Web and Mobile Apps
IOT
Cloud
Network
API
Infrastructure
Possess certifications such as:
OSCP
OSEP
OSWE
OSEE
GXPN
GCPN
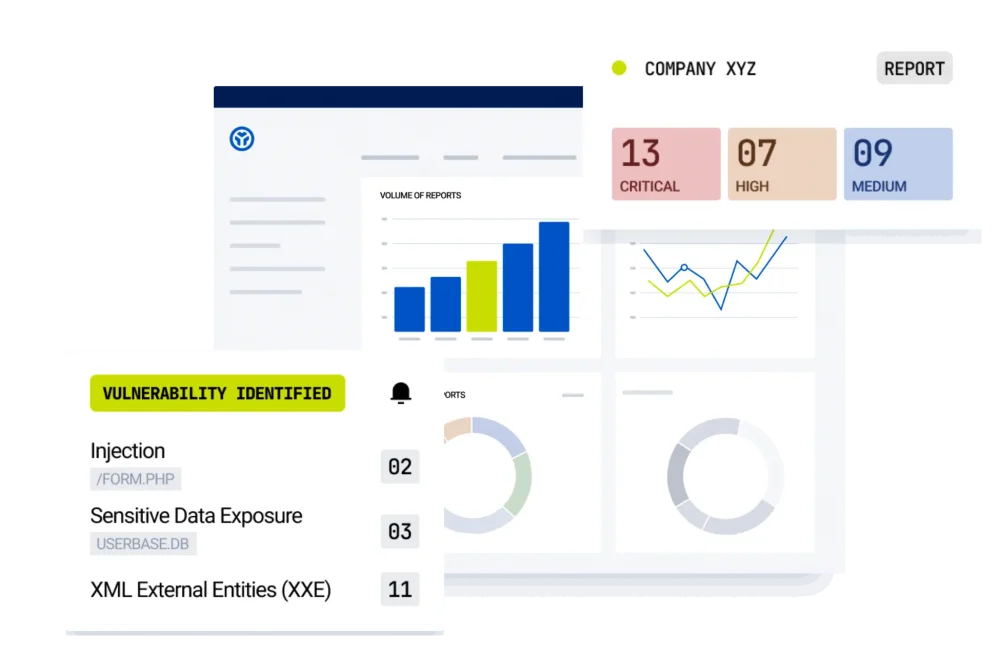
Pentesting management made easy and secure
Offensive Security Testing Platform
- Get notified of critical vulnerabilities
- Real-time overview of risk exposure
- Accelerated remediation
- Vulnerability retest
Ready to pentest your assets?
Uncover vulnerabilities, fortify your defenses, and stay one step ahead of cyber threats.

