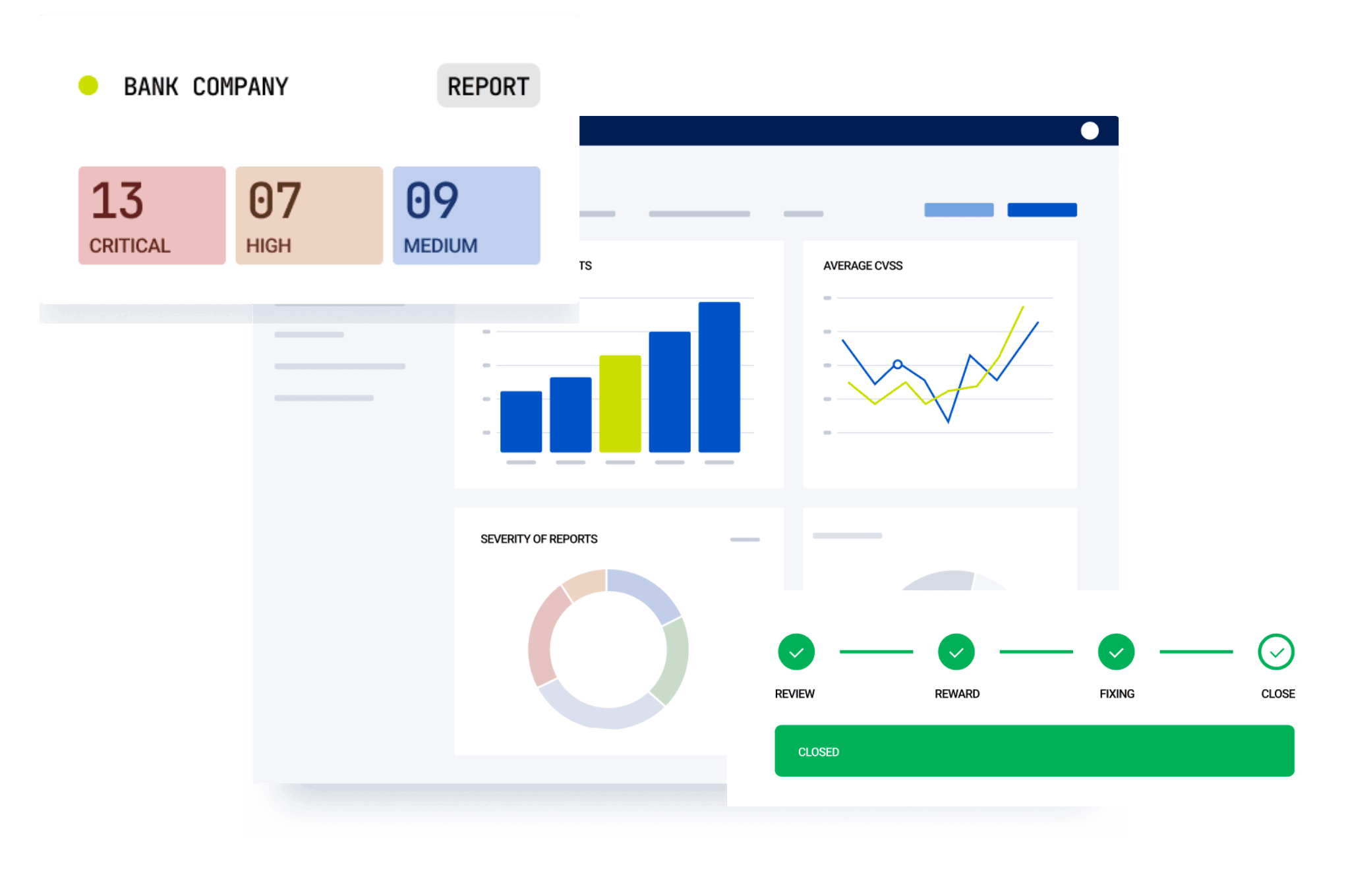
Launch and manage your security tests from end to end — on one platform










One Platform
Multiple Offensive Security Testings
Yogosha’s Offensive Security Testing Platform allows you to uncover and effectively manage critical vulnerabilities with your team and security researchers, from end to end.
Find and manage vulnerabilities with confidence
Our platform empowers more than 300+ security teams across multiple industries.
- Agile Security Testing
- Activity Monitor
- Security Researchers
- SaaS or Self-Hosted
- Multi Workspace
- Real-time Risk Exposure & Analytics
- Security Compliance
- VPN
- Integrations
Launch your security tests within days.
And efficiently and effectively deploy secure assets with each new update. Ideal for DevSecOps.
✅ Made possible with our platform’s security test launch.

Seamlessly assign roles and vulnerability reports.
And delegate tasks extremely fast, from triage to remediation and retest.
✅ Made possible with our 1-click report assignor.

Streamline vulnerability management. From end to end.
And reduce your administrative time for each vulnerability found.
✅ Made possible with our vulnerability report status feature: in 1 click, use different types of statuses from detection, triage and remediation guidance to retest.

Get fully documented vulnerability reports.
And your security / dev teams remediate faster.
✅ Made possible with Yogosha’s standardized report templates including CVSS score, proof of concept with images or videos, and remediation guidance.

Directly communicate with security researchers.
And accelerate vulnerability remediation.
✅ Made possible with our conversational message box.

Monitor security researchers activity on your assets.
And get proof of work and ROI reassurance.
✅ Made possible with our Activity Monitor, including number of researchers at work, working hours, session counts and number of requests.

Get full transparency on the progress of pentests
So you always know what tasks have passed, failed, or not started.
✅ Made possible with Yogosha’s Security Checklist.

Get access to the right security researchers.
And increase the odds in finding critical vulnerabilities.
Continue working with high-performing ones.
✅ Made possible with our vetted community of security researchers, available on demand.

Or invite your own team of security researchers.
And easily onboard them on the Vulnerability Operations Center platform.
✅ Made possible with our invitation program.

Directly communicate with security researchers.
And accelerate vulnerability remediation.
✅ Made possible with our conversational message box.

View profile of selected researchers.
And instill trust between your team and security researchers.
Continue working with high-performing ones.
✅ Made possible with our directory page and researchers’ profile.

SaaS: Securely manage vulnerability reports
And make sure your data is safeguarded.
✅ Made possible with our robust and secure SaaS platform, hosted on 3DS Outscale, certified SecNumCloud. We continuously secure our assets through DevSecOps, OWASP guidelines and a bug bounty / VDP program.

Self-Hosted: Stay sovereign of your data
And keep complete control of all data dealt with such as vulnerability reports submitted on the platform.
✅ Made possible our Self-Hosted solution — on-premise or public / private cloud.

Allow different branches of your organization to run security tests.
And benefit from a unified and centralized experience.
✅ Made possible with our multi-workspace feature.

Supervise, centralize, and compare the risk exposure across your entire organization.
And understand what is going on at all times. Also useful for C-level review.
✅ Made possible with our master workspace.

Limit access to confidential data between workspaces.
And keep control of your data and security testing operations throughout your organization at scale.
✅ Made possible with our permission-invitation system.
Overview risk exposure in real time.
Monitor risk exposure in real time and manage your assets effectively. Find out which are the most fragile, which types of vulnerabilities are most often exploited to reach you, and identify improvement opportunities for your information system and your teams.
✅ Made possible with our dashboard, in-app and email notifications.

Supervise, centralize, and compare the risk exposure across your entire organization.
And understand what is going on at all times. Also useful for C-level review.
✅ Made possible with our master workspace.

Get real-time notifications.
And stay updated every time something important happens.
✅ Made possible with our in-app notification and emailing system and integrations.
Standardize your pentests by requesting security researchers to follow a predefined list of tasks.
And meet compliance requirements and industrialize your pentests.
✅ Made possible with our Security Checklist Catalog.

Easily whitelist security researchers.
And allow researchers to test your assets’ security.
No more false SOC alarms, or firewall problem.
✅ Made possible with the Yogosha VPN.

Instantly transfer vulnerability reports and key data onto your internal tools.
And allocate your time to more crucial tasks.
✅ Made possible our API, integrations and webhooks.

1 Platform
to manage your security tests
48h
to launch a test, not weeks
90%
signal-to-noise ratio
Supported by our Product & Tech teams

"Together, we're not just developing a product, we’re crafting a future where trust in technology isn't just a hope, it's a reality. Every line of code we write, every strategy we deploy, contributes to a safer digital world for all."
Nicolas KALMANOVITZChief Product Officer (CPO)
Explore real-world results
Dive into the success stories of our clients, and discover firsthand how businesses like yours achieved remarkable outcomes in security testing through our platform.
Discover how Groupe ADP, the operator of multiple international airports, deals with security and worked with Yogosha to strengthen it.
Discover how Veepee, an international e-commerce company with more than 3.7 billion in revenue, deals with security and worked with Yogosha to strengthen it.
Discover how Terega, a prominent gaz supplier in Europe with 799 million euros in revenue, deals with security and worked with Yogosha to strengthen it.
Take the next step
Book a personalized demo today and discover how our platform solutions can help you launch and streamline your Offensive Security testings.






